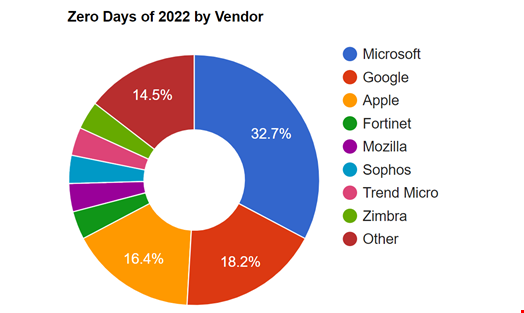
Zero days explained: How unknown vulnerabilities become gateways for attackers
4.7 (689) · € 27.99 · En Stock
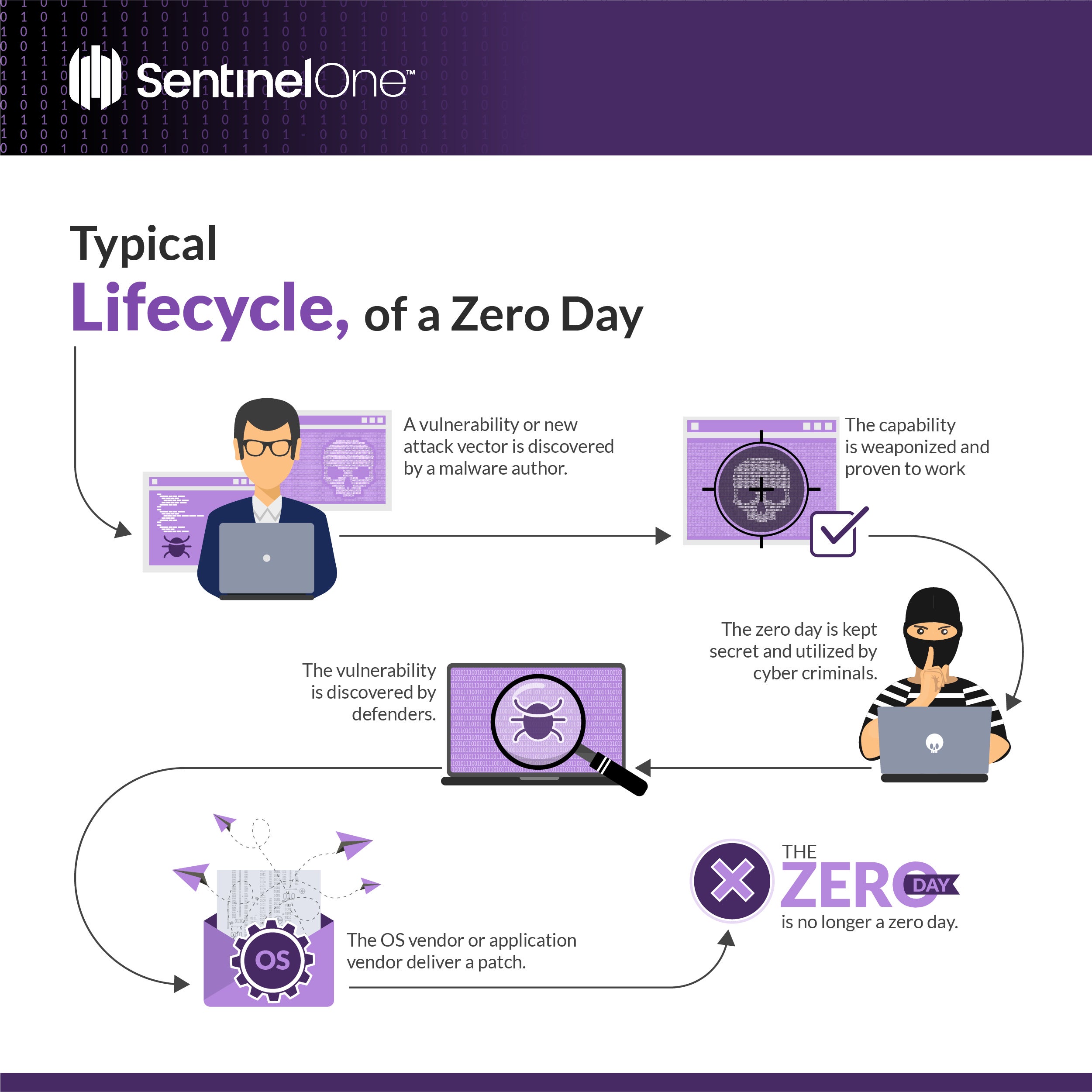
A zero day is a security flaw that has not yet been patched by the vendor and can be exploited. The name evokes a scenario where an attacker has gotten the jump on a software vendor, implementing attacks that exploit the flaw before the good guys of infosec are able to respond.
-1.png?width=600&height=333&name=Zero-day%20attack%20Vs%20(1)-1.png)
5 Security Experts Share Best Practices to Prevent Zero-Day Attacks

From Log4j to Zero Day Exploit: What It Is, Why It Matters, and How to Stop

HTTP/2 Zero-Day vulnerability results in record-breaking DDoS attacks

Zero Day Exploit - IP With Ease
A Guide to Zero-Day Vulnerabilities and Exploits for the Uninitiated - Infosecurity Magazine
Zero-Day Vulnerability: The Unknown Threats to Your Data
Zero-Day Survival Guide, Vulnerabilities & Attacks

What Are Zero Day Attacks? - A Comprehensive Guide

What is a Zero-Day Vulnerability? - 3 Real-World Examples

The Truth About Zero-day Vulnerabilities

Zero-Day Attack - an overview

What is a Zero-Day Exploit, and Why Is It Dangerous?

Security 101: Zero-Day Vulnerabilities and Exploits - Nouvelles de sécurité - Trend Micro FR
Zero-Day Vulnerability: The Unknown Threats to Your Data